LOCH Technology Blog
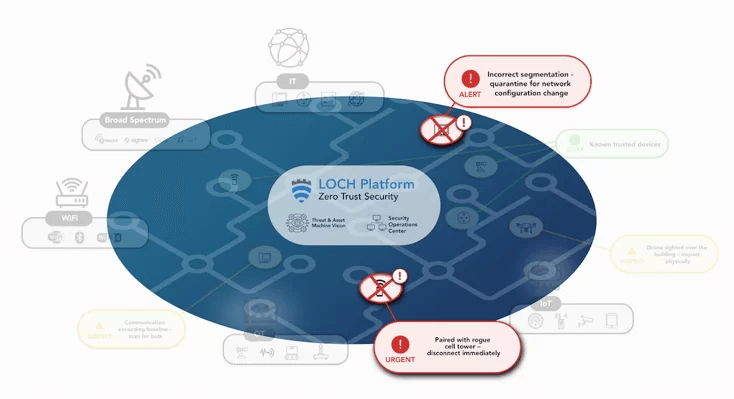
LOCH offers powerful RF intelligence for wireless IT, IoT, IIoT, and OT landscapes, empowering organizations to fortify their security defenses, mitigate risks, and proactively address concealed threats that endanger their business operations.

LOCH breaks onto the INC 5000 List!
LOCH Technologies is thrilled to announce that we have been ranked #1899 on the 2024 Inc. 5000 list for the Fastest-Growing Private Cybersecurity Company.

LOCH Technologies at TechNet Cyber Baltimore 2024
Outpacing the Threat: Align, Adapt, Accelerate Discover LOCH's Unique Approach to Visible Protections Against Invisible Threats at Booth #3356
Unveiling the Vulnerability: Pioneering Cybersecurity in a Connected World
Within the dynamic field of cybersecurity, a paradigm shift is underway. LOCH Technologies is on the forefront of this shift and the need to transition from reactive cybersecurity..

Unveiling the Vulnerability: The Hidden Risks of GPS Networks
In the ever-evolving landscape of technology, we often take for granted the seamless operation of systems that keep our world interconnected. One such cornerstone is the Global..

LOCH 2021 Predictions: Smart Cities, Exponential Wireless IoT Growth, and the Push to Secure the Largest Attack Surface in History
The most unpredictable year in recent memory is at our backs. With that, businesses of all walks are looking to 2021 to assess how significant cybersecurity trends and operational..

Wi-Fi Alliance: The rapid growth of Wi-Fi and the need to secure wireless devices
With digital transformation only accelerating with the Covid-19 pandemic, organizations across industries are looking for ways to support demands for increased wireless..
2024 Wireless Security Predictions
2023 is over, and we are looking forward to all the future has to bring. 2024 promises more cyberattacks than last year; therefore, organizations need to prepare for what's next...
Don’t hand it Over: Vulnerabilities in the Handover Procedure of Cellular Telecommunications
New Mobile Network Vulnerabilities Affect All Cellular Generations Since 2G. Researchers have disclosed security vulnerabilities in handover, a fundamental mechanism that..

A Visionary Leap Forward: Future Proofing Wireless and RF Communications
Read the full article here

