Secure Your Smart City's Wireless Airspace with LOCH's Cutting Edge AI-Powered Defense

LOCH’s Wireless Airspace Defense offers a comprehensive solution to protect smart cities from wireless risks and threats. By leveraging advanced AI and machine learning for real-time detection, assessment, and response, LOCH ensures that smart cities can maintain secure and reliable communications, protect essential mission-critical services, and operate safely in an increasingly connected and digital urban environment.
Wireless Risks and Threats Impacting Smart Cities and Hyperconnectivity
Compromise of IoT Devices and Systems
Threat: Many IoT devices used in smart city infrastructure (e.g., smart meters, traffic sensors, surveillance cameras) are often vulnerable to cyberattacks due to weak security configurations.
Impact: Compromised devices can serve as entry points for broader network attacks, disrupt services (e.g., traffic control, water management), and lead to manipulation of critical infrastructure.
Unauthorized Access to Networks and Data Breaches
Threat: Hackers may gain unauthorized access to smart city networks that rely on Wi-Fi, cellular, IoT, CBRS, and GPS, compromising sensitive data related to citizens, critical infrastructure, or operations.
Impact: Breached data could lead to privacy violations, exposure of confidential information, and potential exploitation for malicious activities or financial gain.
Denial of Service (DoS) & Distributed Denial of Service (DDoS) Attacks
Threat: Attackers can overload smart city networks with malicious traffic, targeting Wi-Fi, cellular, or CBRS networks, rendering mission-critical services inoperable.
Impact: DoS and DDoS attacks can cause significant disruption to essential services, such as emergency response, public transportation, and utility management, impacting citizen safety and city functionality.
Man-in-the-Middle (MitM) Attacks
Threat: Attackers may intercept wireless communications between devices and infrastructure (e.g., GPS signals, Wi-Fi connections) to manipulate data or extract sensitive information.
Impact: This could lead to misinformation, compromised decision-making, and unauthorized access to sensitive city data and systems.
Jamming & Spoofing of GPS & RF Signals
Threat: Jamming or spoofing GPS signals can disrupt location-based services and applications, including emergency response, public safety, and autonomous vehicle navigation.
Impact: Compromised GPS or RF signals can lead to operational delays, safety risks, and potential accidents involving autonomous systems.
Rogue Devices & Access Points
Threat: Malicious actors could deploy rogue devices or access points to mimic legitimate networks, tricking city employees or citizens into connecting to them and revealing sensitive information.
Impact: This could result in data breaches, unauthorized access, and further propagation of malicious software or attacks.
Cyber-Physical Attacks on Infrastructure
Threat: Exploitation of wireless vulnerabilities to launch cyber-physical attacks that target the physical components of smart city infrastructure (e.g., power grids, water supply systems).
Impact: Such attacks can result in significant physical damage, service outages, and public safety hazards, requiring costly repairs and potentially putting lives at risk.
Potential Impacts on Business Operations for Smart City Initiatives
Service Disruption & Operational Downtime
Wireless attacks can disrupt mission-critical services, such as traffic management, public safety communications, utility services, and emergency response, leading to operational downtime and safety risks.
Public Safety & Security Risks
Compromised wireless communications can impact the safety and security of citizens, especially if critical systems (e.g., emergency services, surveillance systems) are affected by attacks.
Decreased Efficiency & Productivity
Wireless threats can impact the efficiency of smart city operations, reducing productivity and increasing the complexity and cost of managing urban infrastructure.
Financial Losses & Increased Costs
Cyberattacks and data breaches can lead to significant financial losses due to service disruptions, incident response costs, legal liabilities, and fines for non-compliance with regulatory standards.
Reputation Damage & Loss of Public Trust
Security breaches can erode public trust in smart city technologies and initiatives, potentially hindering future adoption and collaboration with private sector partners.
Regulatory Compliance Violations
Failure to protect wireless networks and communications can result in non-compliance with industry regulations and standards, leading to penalties, increased scrutiny from regulators, and potential loss of operational licenses.
How LOCH Wireless Airspace Defense Can Mitigate Risks Across Smart City Infrastructures
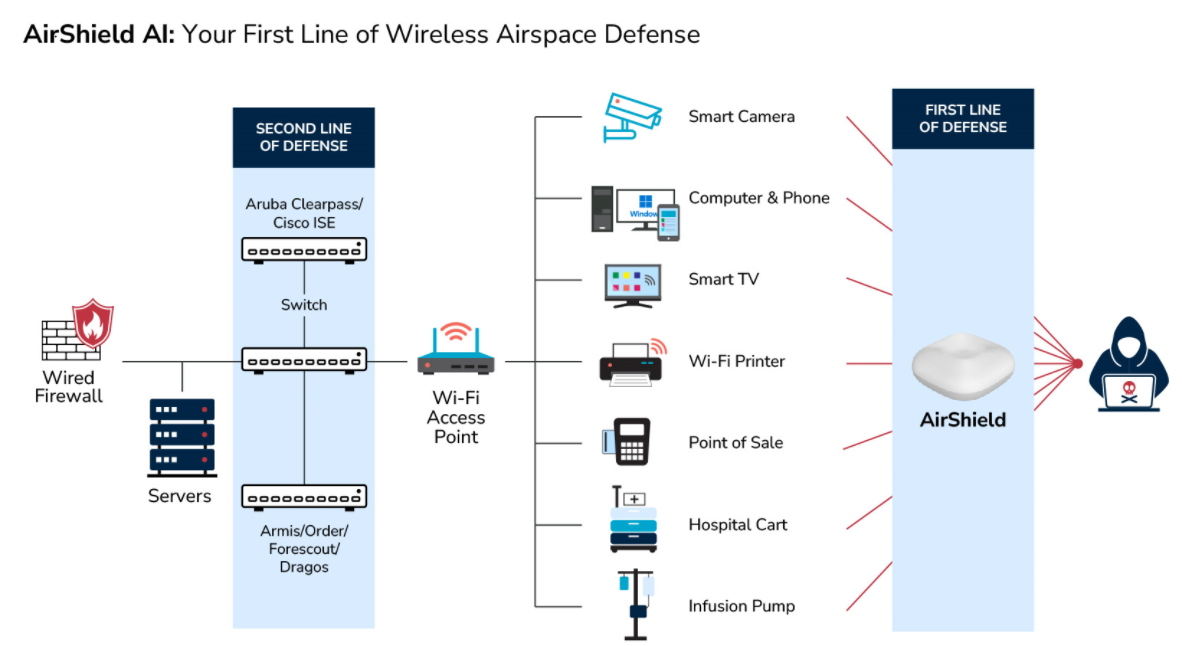
Real-Time Monitoring and Threat Detection
Capability: Continuous monitoring of wireless signals across Wi-Fi, cellular, IoT, CBRS, and GPS spectrums to detect unauthorized devices, rogue access points, and abnormal signal activities.
Benefit: Early detection of potential threats allows for quick response, minimizing the risk of successful attacks and ensuring the integrity of critical services.
AI-Driven Anomaly Detection and Response
Capability: Leverages AI and machine learning algorithms to detect anomalies in wireless traffic patterns, identify potential security threats, and initiate automated responses.
Benefit: Provides proactive threat detection and response capabilities, helping to prevent unauthorized access, mitigate risks, and maintain operational continuity.
Automated Threat Mitigation and Incident Response
Capability: Automatically isolates and neutralizes detected threats, such as blocking rogue devices, mitigating jamming attempts, or preventing unauthorized access without manual intervention.
Benefit: Rapid threat response reduces potential damage, ensures the continuity of mission-critical services, and enhances overall network security.
Integration with Existing Healthcare Security Systems
Benefit: Reduces the risk of unauthorized access, insider threats, and rogue device exploitation, enhancing the overall security posture of smart city operations.
Integration with Existing Smart City Security Frameworks
Capability: Seamlessly integrates with existing smart city cybersecurity frameworks and infrastructure, providing a unified approach to wireless security.
Benefit: Enhances overall security without requiring significant changes to current systems, ensuring consistent protection across all operational areas.
Continuous Reporting and Compliance Support
Capability: Provides detailed reports on wireless activity and incidents, supporting regulatory compliance, post-incident analysis, and continuous improvement in security strategies.
Benefit: Helps maintain compliance with industry regulations, reduces the risk of legal penalties, and supports smart city resilience and sustainability efforts.
Protection Against Cyber-Physical Attacks
Capability: Monitors for anomalies that could indicate attempted cyber-physical attacks, such as unauthorized control signals or equipment malfunctions triggered via wireless channels.
Benefit: Helps prevent attacks that could cause physical damage to infrastructure, ensuring the safety and security of both citizens and critical city assets.
- - Detect, identify and classify all broad spectrum RF emitting devices in range
- - Device and network pairing communication map analysis and correlation
- - Risk assessment threat ranking for Zero Trust network access control
- - Mobile App for hunting rogues even if mobile
- - Wireless deep packet inspection
- - Behavioral baselining, analysis and anomaly detection/alerts
- - DVR-like capabilities for forensics, including geo-positioning
- - Carrier integration with cell. devices for anomaly detection, fraud/theft and cost management
- - List and map devices on dashboard or into SIEMs.
- - Interact with MDM and EMM assets for correlation and feedback on exceptions
- - Rectify network segmentation via interactions with SOAR, FW and/or NAC systems
- - Automate response and closure via collaboration with ITSM/ITSL and CMDBs