2024 Wireless Security Predictions
2023 is over, and we are looking forward to all the future has to bring. 2024 promises more cyberattacks than last year; therefore, organizations need to prepare for what's next. In this new 2024 Wireless Security Predictions report, we provide insights into the new external attack surface of wireless - the invisible threat.
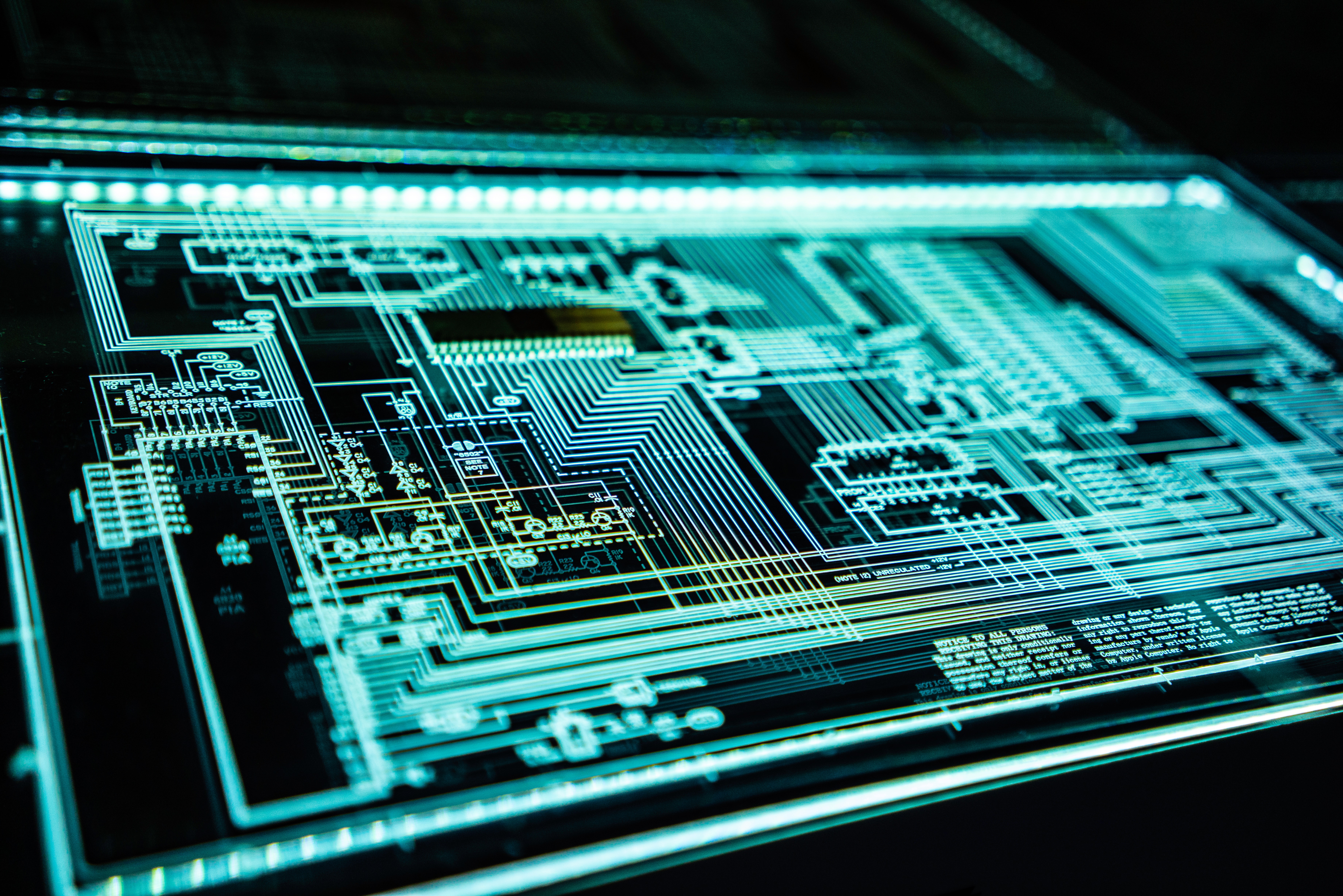
The world is changing, and soon, everything will be connected wirelessly.
The Internet of Things (IoT) has created the world’s largest and most vulnerable attack surface, the scope of which is only broadening with the promise of 5G. Today’s networks and organizations were never built to handle the extraordinary volume, velocity, and hyperconnectivity of IoT technologies in the modern enterprise.
With 80% of new IoT devices wirelessly connected, wireless has quickly become the new network and new attack surface - the invisible threat.
Top Trending Wireless Threats
1. 5G Network Security: With the widespread adoption of 5G, concerns about the security of these networks will continue to grow. Issues such as privacy breaches, data interception, and network infrastructure attacks are likely to be prominent.-
- Data Interception of 5G networks is more susceptible to eavesdropping due to the use of higher frequency bands. Monitoring beyond the WiFi frequencies is essential in today’s environment as Hackers may attempt to intercept sensitive data, posing a significant threat to user privacy and data security. Implementing end-to-end encryption is vital to mitigate this risk.
-
- Emerging Threats: With the evolution of IoT technology, new and evolving threats will emerge. Staying updated on the latest threat intelligence and continuously assessing and improving security measures across the mot commonly used frequencies used by IoT will be crucial.
-
- With LOCH's recent acquisition of Avirtek for Self-Protection of critical networks, the Avirtek technology provides the ability to offer 'Autonomic' (self-protection) capabilities with intelligent automated responses, removing the human out of the loop. Avirtek's Data Behavior Analysis leverages Autoencoder ML to learn data traffic patterns, irrespective of the data being encrypted or not. This approach eliminates the 'people' factor as the weakest link in the kill-chain. Moreover, its instantaneous design ensures immediate, proactive responses with zero-day protection, ensuring robust and efficient security.
-
- Ensuring the security of the entire supply chain from 5G, broad-spectrum, and WiFi network components is essential. Malicious actors may attempt to infiltrate the supply chain to compromise hardware or software components, which can have far-reaching consequences.
-
- Network segmentation, multi-factor authentication (MFA), encryption, and regular security assessment will be key going forward. Implementation of an outside-in scanning regiment is now important in order to understand the NEW external attack surface.
-
- Handling insider threats requires a combination of technical controls, employee education, and proactive monitoring. Implementing these security measures, such as Access Control, User Authentication and Authorization, Employee Training and Awareness, Monitoring and Logging, Behavior Analytics, and Endpoint Security, will foster a culture of security within your organization that can better protect your wireless network against insider threats.
-
- With the increased speed and capacity of 5G networks, there's a higher potential for privacy breaches. Personal data transmitted over 5G networks may be vulnerable to interception and misuse. It's crucial to ensure robust encryption and authentication mechanisms are in place.
