AirSnitch: A New Wi-Fi Attack Shows Encryption Alone Isn’t Enough
A newly disclosed attack called AirSnitch highlights a growing reality in wireless security: even modern encryption standards like WPA2 and WPA3 cannot fully protect wireless environments from attacks occurring in the wireless airspace.
Researchers demonstrated how AirSnitch can bypass Wi-Fi client isolation protections, allowing attackers to perform a bidirectional Man-in-the-Middle (MitM) attack across home, enterprise, and public Wi-Fi networks.
The key lesson is clear: encryption alone is not enough to secure wireless environments. Organizations must also secure the wireless airspace itself.
How the AirSnitch Attack Works
AirSnitch does not break Wi-Fi encryption directly. Instead, it exploits weaknesses in client isolation mechanisms and MAC address handling within access points.
By spoofing a victim’s MAC address and manipulating network mappings using ICMP messages and valid GTK keys, an attacker can intercept both uplink and downlink traffic, effectively placing themselves between the user and the access point.
The result: full interception of wireless communications even when WPA2 or WPA3 encryption is enabled.
Researchers identified multiple vulnerable device platforms, and some may require hardware-level fixes rather than simple firmware patches.

Join Us at the Security & Policing Home Office Event – Farnborough, UK, March 11th - 13th, 2025
Read More
Creating the Next Frontier in Wireless Technology: The Critical Need for Wireless Airspace Defense
Read More
The Silent Threat of Rogue Wi-Fi Networks on Navy Ships – How LOCH's AirShield Could Have Prevented a Security Breach
Read MoreThe Bigger Lesson for Enterprise Security
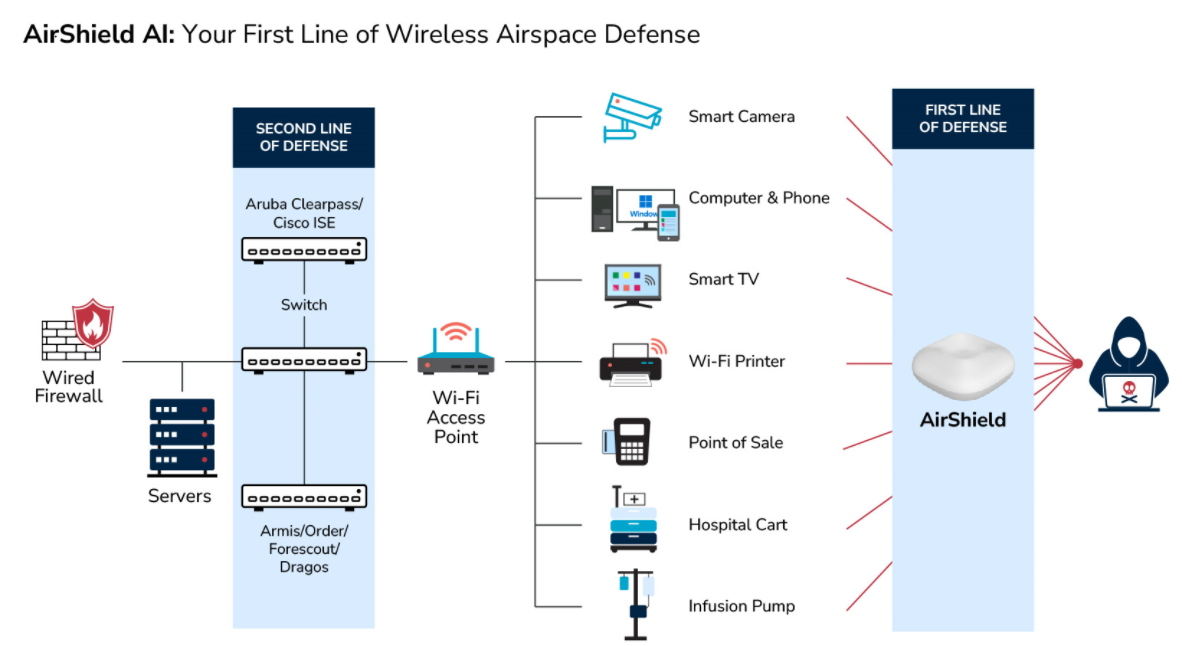
AirSnitch exposes a major blind spot in many enterprise security architectures.
Most organizations assume that Wi-Fi encryption protects the network, but attacks like AirSnitch operate directly in the wireless layer, where traditional security tools—such as firewalls, endpoint protection, and network monitoring—have limited visibility.
Without continuous monitoring of the wireless environment, these attacks can remain undetected for extended periods.
Securing the Wireless Airspace
Protecting modern wireless networks requires visibility into the wireless attack surface, including the ability to:
-
Detect MAC spoofing and identity manipulation
-
Identify rogue devices and rogue infrastructure
-
Monitor wireless activity continuously
-
Detect anomalous wireless behavior in real time
This is where wireless airspace defense becomes essential.
How AirShield Helps
LOCH’s AirShield provides continuous monitoring and intelligence across the wireless airspace, enabling organizations to detect and respond to sophisticated wireless threats that bypass traditional network defenses.

AirShield provides 24/7 persistent monitoring of the wireless airspace, delivering real-time detection, assessment, and prevention of threats across cellular, IoT, Wi-Fi, Bluetooth, and GPS/satellite networks—securing the full wireless attack surface.
About LOCH Technologies
LOCH Technologies, Inc. is a global leader in innovative threat monitoring, detection, and mitigation.
Our cutting-edge ACS solution deliver actionable intelligence on every Device, Network, or Thing, empowering organizations to enhance their security posture and eliminate risk.
At LOCH, our mission is to secure and enable the new world of innovation driving the next generation of digital transformation. We are committed to protecting the digital ecosystem, ensuring a safer and more resilient future for businesses and communities worldwide.