Discover the Hidden Threats: Implement Robust Wireless Airspace Defense to Enforce Zero-Trust

Fortifying the Stadium of the Future: RF Defense for Fans, Players, and Infrastructure
Learn how to protect your stadium from invisible threats impacting fans, players, and infrastructure.

We made the 2024 & 2025 Fastest Growing Companies in America list!
Thank you, Thank you, Thank you!
Protect Your Port & Stay Compliant with the Latest USCG Standards
We bring our AI to secure your data, to stop what others cannot.






The accelerated adoption of digital transformation, with a connected-everything approach, has created another potential target for cyberattacks. IT systems and ICS/OT systems are no longer separate entities, and using different cybersecurity tools for each system is no longer enough to ensure comprehensive protection.
What is Autonomic Cyber Security (ACS)?
Autonomic Cyber Security is an advanced cybersecurity framework designed to automatically detect, respond to, and mitigate cyber threats in real time. Leveraging AI and machine learning.
ACS aims to provide a self-managing security environment that adapts to evolving threats without human intervention.
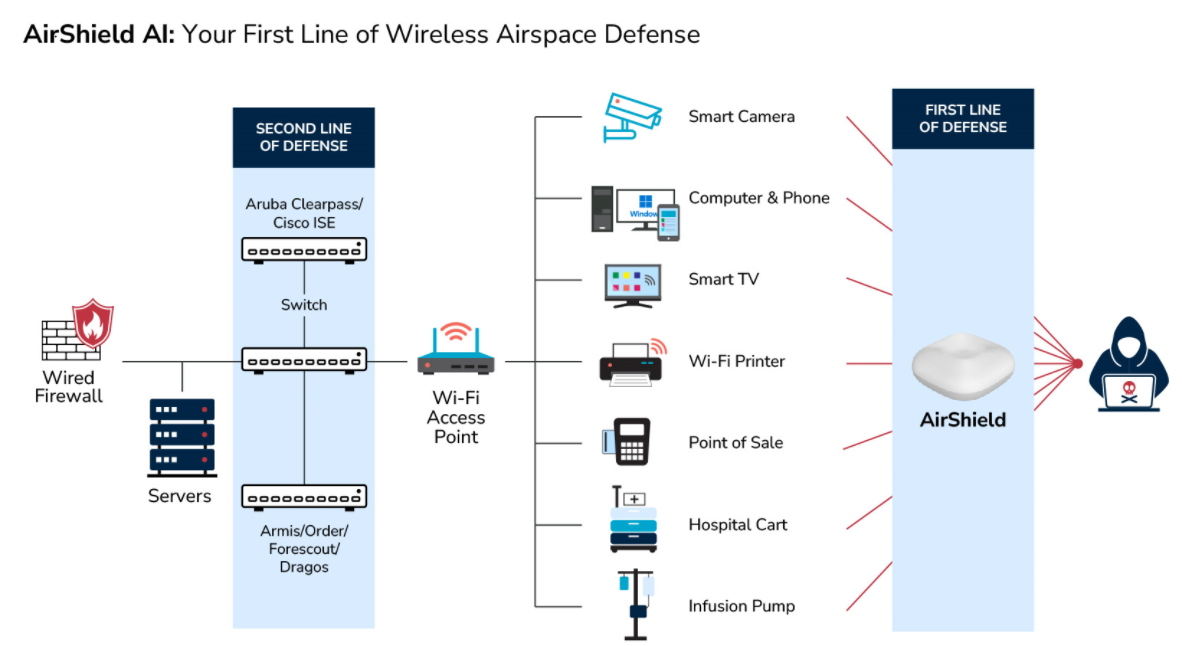
What is Wireless Airspace Defense?
Wireless Airspace Defense is a comprehensive security platform designed to protect wireless networks and devices from unauthorized or malicious activities.
This system leverages advanced technologies like software-defined radios (SDRs), AI, and machine learning to provide real-time threat detection, monitoring, and response before a loss or incident occurs.

 mentions LOCH Technologies 25 times and counting...
mentions LOCH Technologies 25 times and counting...
- Market Guide for Medical Device Security Solutions, December 2020
- Emerging Technologies and Trends Impact Radar: Security, October 2021
- Emerging Technologies and Trends Impact Radar: Internet of Things, September 2021
- Security Service Providers: Time to Capitalize on IoT and Operational Technology, May 2021
- Cool Vendor in Edge Computing, May 2021
- Market Guide for Operational Technology Security, Jan 2021
- Invest Implications: Emerging Tech Impact Radar: Security, November 2022
- Emerging Tech Impact Radar: Security, November 2022
- Market Guide for Medical Device Security Solutions, March 2022
- Emerging Tech: Security – Venture Capital Growth Insights for Cyber-Physical Systems Security, June 2023
- Market Guide for Medical Device Security Solutions, April 2023
- Emerging Tech: Why the Need for Wireless Airspace Defense, Jan 2024
- Market Guide for Medical Device Risk Management Platforms, Aug 2024