The LOCH Wireless AI Machine Vision platform enables organizations to discover, track, monitor, and help manage ALL wireless, broad-spectrum RF and 4G/5G IoT devices.
The Internet of Things (IoT) are individually addressable physical objects with sensors, processing ability, software, and other technologies that connect and exchange data with other devices and systems over the Internet or other communications networks.
27B+ such devices are expected to be deployed worldwide by 2025 with over 80% using traditional 802.11 WiFi, BT/BLE, Broad Spectrum RF (30MHz – 6GHz) and/or public or private 4G/LTE/5G.
IoT Challenges:
- The sheer volume and scale involved – devices, OS/Protocols, connectivity and security
- Use of broad-spectrum RF for communications – none or limited visibility for ‘wired’ security solutions
- Sifting through the good (protect known devices), bad (quarantine and fix compromised devices) and the ugly (terminate nefarious and covert surveillance/theft devices)
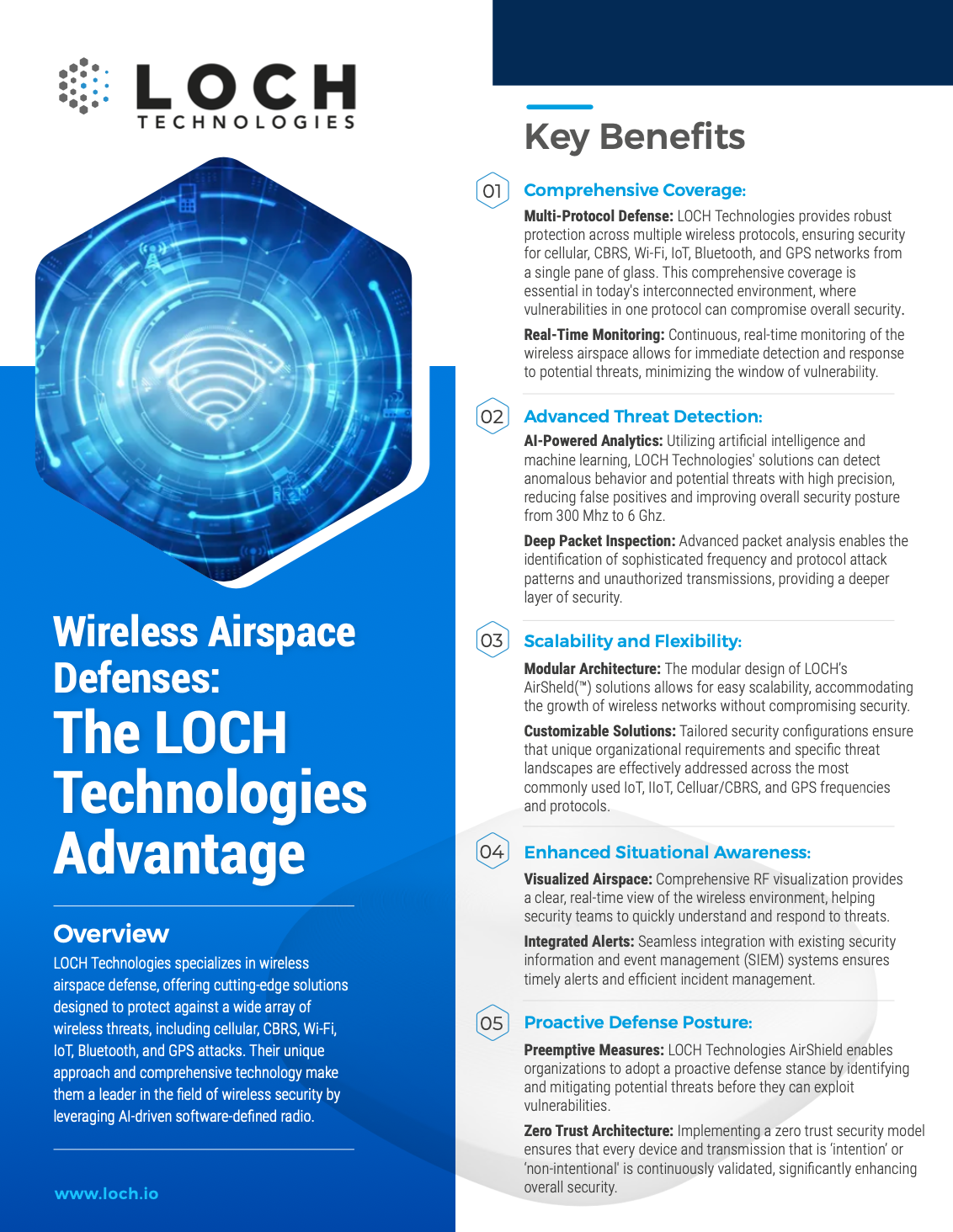
LOCH helps bring order to the new wireless chaos with its patented Wireless AI Machine Vision platform comprising of AirShield℠, AirCell℠ and AirGuard℠; providing non-intrusive 24×7 real-time visibility and comprehensive protection for IoT, Industrial Internet of Things (IIoT), Internet of Medical Things (IoMT) devices across enterprise and mission-critical environments regardless of operating system, protocol, communications frequency or connection type.
LOCH delivers a Zero Trust Framework for proactive security posture management combining Software Defined Radios and Machine Learning Wireless Analytics. This framework ensures the environment is protected against rogue actors, misconfigured devices, and covert data exfiltration paths – the new and invisible Wireless Attack Surface.
Benefits of the AirCell
Benefits of the AirShield
AirShield℠ provides non-intrusive real-time visibility and comprehensive monitoring and protection for broad-spectrum wireless devices for IoT, Industrial Internet of Things (IIOT), Internet of Medical Things (IOMT), irrespective of operating system, protocol, or connection type. With its software-defined radios, AirShield monitors an organization’s entire airspace to ensure the environment is protected against rogue devices, misconfigured devices, and previously undetected wireless threats.
Benefits of the AirGuard
The Wireless AI Machine Vision™ Platform
The LOCH Wireless AI Machine Vision Platform provides actionable intelligence and insight for all 5G cellular and broad-spectrum wireless IoT devices.
LOCH Technologies Wireless Cybersecurity Solutions
Resources

Sales Partners
The Support You Need To Successfully Deploy Solutions From LOCH Technologies